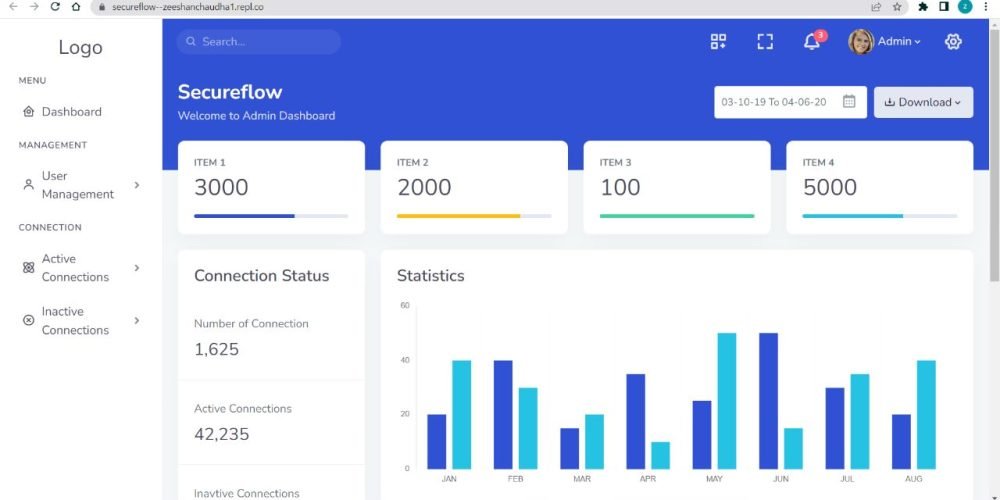
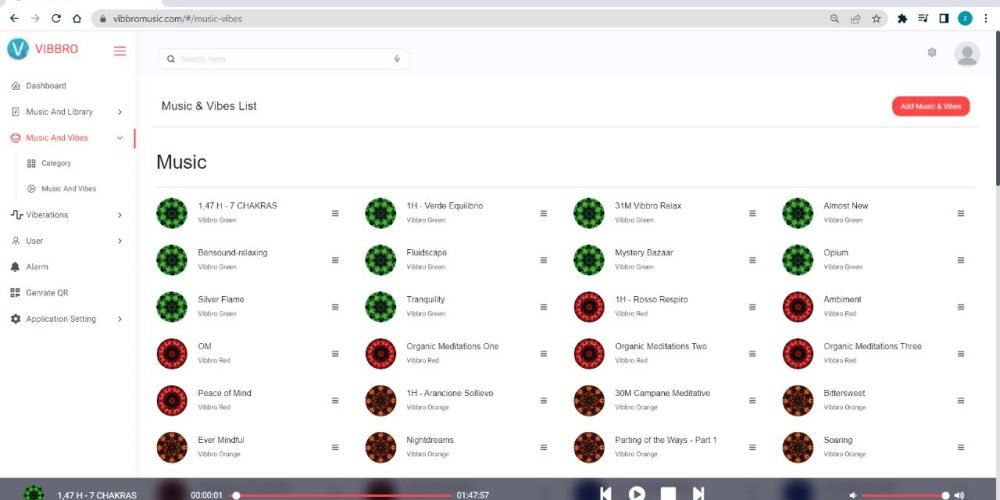
Identity Access Management (IAM) forms the basis of a Zero Trust approach to cybersecurity. Traditional network perimeters are no longer effective in securing assets distributed across multiple clouds. Digital Risk Management (DRM) and the shift to a Zero Trust approach shift security from being based on perimeters to being based on identities, safeguarding data and services. A comprehensive Zero Trust architecture should encompass all aspects, from end users to specific applications and services, and should have the capability to define who, when, where, and how access is granted. The aim is to verify and authenticate identity PRIOR to granting access, thereby preventing hacking, ransomware, and resisting attacks.
With Zero Trust Zone Protected Perimeter, all network attacks are thwarted by allowing ONLY authorized and verified end users to have permissioned access to the protected application or service contained within the Trust Zone(s).